Building measurable data security capabilities for your organization
In a data-driven business world, data security directly affects trust, compliance, and business continuity. Raresoft's data security services are risk-driven and combine technology, processes, and people to help organizations identify sensitive data, design protection strategies, and implement controls—reducing the risk of data leakage, tampering, and loss.

We apply end-to-end encryption for both data at rest and data in transit, using industry-standard algorithms and rigorous key lifecycle management. With layered and column-level encryption, sensitive data remains unreadable even if it falls into the wrong hands, significantly enhancing overall data protection.
We deploy content-aware DLP policies to monitor channels such as email, cloud storage, web uploads, printing, and removable media (e.g., USB). Sensitive data is detected, blocked, and alerted in real time to ensure effective protection across internal and external pathways.
We implement identity-based access management (IAM) and the principle of least privilege to manage the lifecycle of users, devices, and service accounts. Privileged account controls and access auditing ensure only authorized principals can reach sensitive data.
We establish strong authentication mechanisms—such as multi-factor authentication (MFA) and certificate-based authentication—to prevent account takeover or unauthorized access due to credential compromise. Session controls and risk-aware authentication further raise the security posture.
We log and monitor data access, transfers, and operations in real time. By integrating SIEM/SOAR and behavior analytics (UEBA), we detect anomalies, trace incidents, and enable rapid response—shortening the window of exposure.
Aligning with your business context and regulatory requirements (for example, data classification, GDPR, or national network security standards), we design practical security controls and audit processes to help your organization meet compliance while protecting data effectively.
Comprehensive Data Security Service Catalog
Endpoint & Device Security: Deploy data protection and access controls on desktops, mobile devices, and IoT endpoints. Combined with device management and patch management, this reduces the attack surface.
Network & Cloud Security: Protect data in transit and storage across hybrid cloud environments using micro-segmentation, zero trust network access (ZTNA), and cloud security configuration assessments.
Identity & Access Management (IAM): Enforce role-based least privilege, single sign-on (SSO), multi-factor authentication (MFA), and privileged access management so only authorized entities access sensitive data.
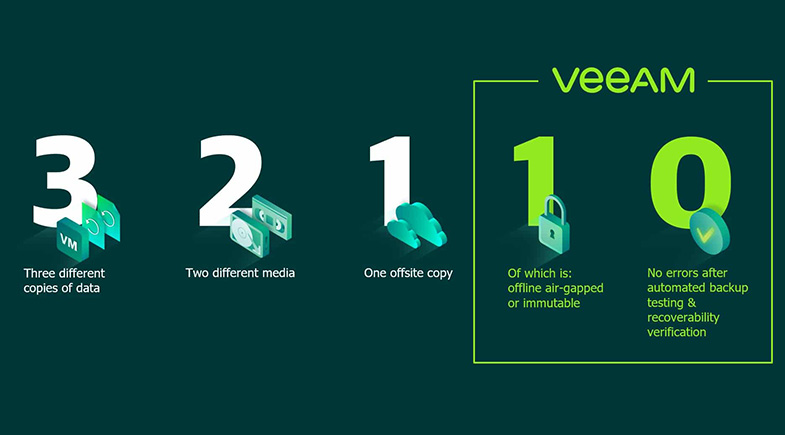
Backup & Disaster Recovery: Implement tiered and encrypted backup strategies and conduct regular recovery drills to ensure fast restoration of business operations and data integrity after incidents or ransomware events.
Security Operations & Response (SOC): Deliver 24/7 security monitoring, incident investigation, forensics, and rapid response to shorten detection and response times and minimize impact.